Microsoft 365 Security Audit
Office 365 Email, Identity & Compliance
Most businesses rely on Microsoft 365 (Office 365) for email, collaboration, document storage, and communication, but without a proper security audit, your data, users, and reputation may be at risk.
A comprehensive security audit goes beyond basic checks, it identifies hidden misconfigurations, security gaps, and compliance blind spots that could expose your organization to cyber threats.
✅ Identity, MFA & Conditional Access Review
✅ Azure AD User, Role & Privileged Access Assessment
✅ Email Security, Anti-Phishing & Threat Protection Review
✅ Data Protection, DLP & Information Governance Analysis
✅ Secure Configuration of Microsoft 365 Workloads
✅ Risk-Rated Findings with Actionable Remediation Plan
Email Security & Microsoft 365 Security Services in Orange County, CA
OC Security Audit provides email security and Microsoft 365 security services throughout Orange County, California.
We support businesses in Irvine, Anaheim, Santa Ana, Costa Mesa, Newport Beach, Huntington Beach, Fullerton, Orange, Garden Grove, Mission Viejo, other cities throughout Orange County, and Los Angeles County, Long Beach.



949-777-5567
Support@OCsecurityAudit.com
Irvine, California
✅ Identify Hidden Security Gaps
Uncover misconfigurations in identity, email, data protection, and access controls that attackers commonly exploit in Microsoft 365 environments.
✅ Strengthen Email & Phishing Protection
Review SPF, DKIM, DMARC, anti-phishing, Safe Links, and Safe Attachments to reduce business email compromise (BEC) and malware risk.
✅ Secure Identities with MFA & Conditional Access
Validate multi-factor authentication, privileged access, and policy enforcement to prevent account takeovers and unauthorized access.
✅ Protect Sensitive Data & Compliance Posture
Assess encryption, sensitivity labels, data loss prevention (DLP), and retention policies to support HIPAA, SOC 2, ISO, and regulatory requirements.
✅ Deliver a Clear Remediation Roadmap
Receive a prioritized, actionable report with risk ratings and step-by-step recommendations — not just findings.
✅ Microsoft 365 Is the #1 Target for Phishing Attacks
Attackers specifically target Microsoft 365 users to steal credentials and bypass weak email protections.
Without proper configuration, phishing emails often reach user inboxes unnoticed.
✅ Stolen Credentials Enable Silent Account Takeovers
Compromised passwords allow attackers to log in without triggering alerts or suspicion.
Lack of MFA and Conditional Access makes these attacks extremely effective.
✅ Business Email Compromise Causes Financial Fraud
Threat actors impersonate executives and vendors to redirect payments or steal sensitive data.
These attacks often bypass basic spam filtering and exploit trusted email relationships.
✅ Misconfigured Security Settings Create Hidden Exposure
Default Microsoft 365 settings are not designed for maximum security.
Misconfigurations in identity, sharing, and email policies leave organizations vulnerable.
✅ Compliance Failures Lead to Fines and Data Breaches
Improper data protection and logging can result in regulatory violations and audit failures.
Security gaps often go unnoticed until after a breach or compliance investigation.
✅ Identity & Access Management (IAM)
Controls user authentication, permissions, and access to Microsoft 365 resources.
✅ Multi-Factor Authentication (MFA)
Prevents unauthorized access by requiring additional verification beyond passwords.
✅ Conditional Access Policies
Enforces access rules based on risk level, device compliance, and user location.
✅ Privileged Identity Management (PIM)
Limits standing admin access and enforces just-in-time privilege elevation.
✅ Email Security & Anti-Phishing Protection
Protects Exchange Online from phishing, malware, and business email compromise attacks.
✅ SPF, DKIM, and DMARC Configuration
Validates sender authenticity and reduces email spoofing and domain abuse.
949-777-5567
Support@OCsecurityAudit.com
Irvine, California
✅ Microsoft Defender for Office 365
Provides advanced threat protection for links, attachments, and collaboration tools.
✅ Data Loss Prevention (DLP)
Prevents sensitive data from being shared or leaked outside the organization.
✅ Sensitivity Labels & Information Protection
Classifies and encrypts data based on business and compliance requirements.
✅ Audit Logging & Activity Monitoring
Tracks user and admin actions for security investigations and compliance.
✅ Device & Endpoint Management (Intune)
Ensures only compliant and secure devices access Microsoft 365 services.
✅ Compliance & Governance Controls
Supports regulatory requirements such as HIPAA, SOC 2, ISO, and NIST.
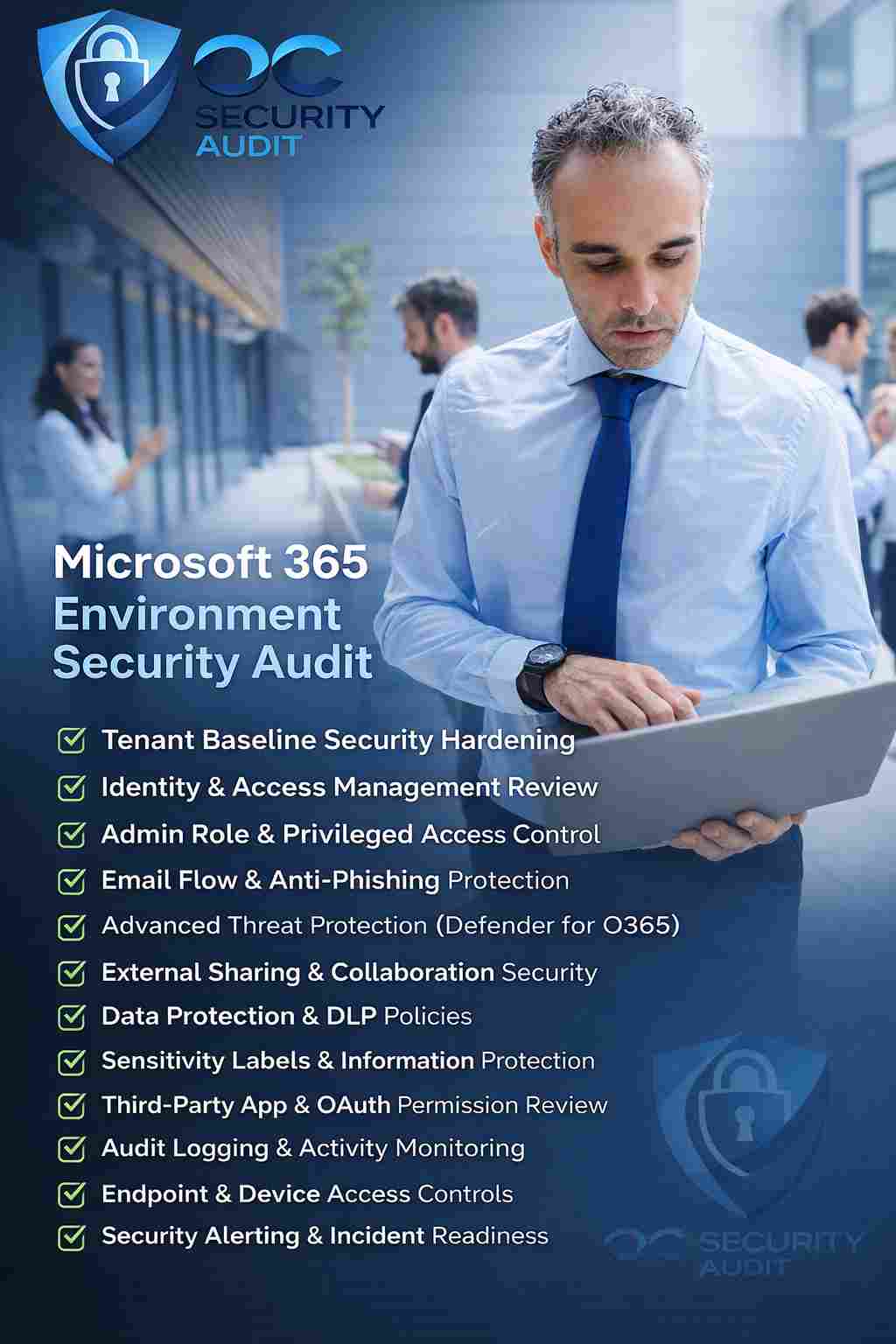
✅ Tenant Baseline Security Hardening
Ensure default Microsoft 365 settings are aligned with security best practices.
✅ Identity & Access Management Review
Validate MFA, Conditional Access, and least-privilege access for all users.
✅ Admin Role & Privileged Access Control
Eliminate excessive admin rights and enforce just-in-time privilege elevation.
✅ Email Flow & Anti-Phishing Protection
Secure Exchange Online with SPF, DKIM, DMARC, and Defender policies.
✅ Advanced Threat Protection (Defender for O365)
Protect users from malicious links, attachments, and zero-day threats.
✅ External Sharing & Collaboration Security
Control SharePoint, OneDrive, and Teams sharing to prevent data leakage.
✅ Data Protection & DLP Policies
Safeguard sensitive data using DLP, encryption, and retention controls.
✅ Sensitivity Labels & Information Protection
Classify and encrypt business-critical information automatically.
✅ Third-Party App & OAuth Permission Review
Identify and remove risky applications and excessive API permissions.
✅ Audit Logging & Activity Monitoring
Ensure logs are enabled for forensic investigations and compliance needs.
✅ SPF Record Configuration & Validation
Ensures only authorized mail servers can send email on behalf of your domain.
Reduces spoofing and improves email deliverability.
✅ DKIM Email Signing Enablement
Digitally signs outgoing email to verify message integrity and authenticity.
Prevents tampering and increases trust with recipient mail systems.
✅ DMARC Policy Enforcement (Quarantine/Reject)
Defines how receiving servers handle unauthenticated messages.
Protects your domain from phishing and impersonation attacks.
✅ Anti-Spam & Anti-Malware Policy Hardening
Blocks malicious and unwanted messages before they reach user inboxes.
Reduces exposure to ransomware and malicious payloads.
✅ Anti-Phishing & Impersonation Protection
Detects credential harvesting and executive impersonation attempts.
Helps prevent business email compromise and fraud.
✅ Microsoft Defender Safe Links Protection
Scans and rewrites URLs to protect users from malicious links.
Provides real-time protection when links are clicked.
✅ Microsoft Defender Safe Attachments Protection
Analyzes attachments in a secure sandbox environment.
Stops zero-day malware and weaponized files.
949-777-5567
Support@OCsecurityAudit.com
Irvine, California
What Is Email Encryption & How It Works
✅ Protects Email Content from Unauthorized Access
Email encryption ensures message content cannot be read by unintended recipients.
Only authorized users with proper authentication can access the message.
✅ Encrypts Messages Both In Transit and At Rest
Encryption protects emails while they are being sent and while stored in mailboxes.
This reduces the risk of interception or unauthorized access at any stage.
✅ Prevents Data Interception and Eavesdropping
Encrypted emails cannot be read if intercepted by attackers or third parties.
This is critical when sending sensitive or confidential information.
✅ Ensures Only Intended Recipients Can Read Emails
Recipients must verify their identity before accessing encrypted messages.
This prevents accidental exposure if emails are forwarded or misdelivered.
✅ Supports Regulatory and Compliance Requirements
Email encryption helps meet requirements for HIPAA, SOC 2, ISO, and other standards.
It demonstrates due diligence in protecting sensitive communications.
✅ Reduces Risk of Data Leaks and Breaches
Encryption minimizes the impact of compromised accounts or stolen emails.
Even if accessed, encrypted data remains unreadable to attackers.
Risk Assessment & Governance Audit – Evaluates organizational risks and the effectiveness of governance, policies, and decision-making frameworks.
Internal Security Audit – Reviews internal controls, processes, and systems to ensure compliance and security best practices.
External Security Audit – Assesses security posture against external threats, standards, and regulatory requirements using independent evaluation.
Network Vulnerability Assessment – Identifies weaknesses in network infrastructure that could be exploited by attackers.
Cloud Security Audit – Examines cloud environments to ensure configurations, access controls, and data protections are secure and compliant.
949-777-5567
Support@OCsecurityAudit.com
Irvine, California
Security Audit for Microsoft 365 Review
Comprehensive, Multi-point Security Review
- Multi-Factor Authentication (MFA)
- Privileged Account Usage
- Email Security Policies
- SPF, DKIM & DMARC Configuration
- Audit Logging & Alert Policies
- Data Loss Prevention (DLP) Settings
- External Sharing Controls
- Secure Score & Baseline Comparison
- Mailbox & Calendar Permissions
- Inactive & Stale Accounts

949-777-5567
Support@OCsecurityAudit.com
Irvine, California

A structured approach to identifying and resolving security risks in your Microsoft 365 environment.
- Define Scope and Objectives
- Collect and Analyze Security Configurations
- Identity & Access Management Audit
- Email & Messaging Security Review
- Data Protection and Compliance Review
- Sharing & Collaboration Risk Review
- Audit Logs and Alerting Readiness
- Secure Score Assessment
- Report Findings and Prioritized Recommendations
- Support Remediation and Continuous Improvement
Items to Check
User role assignments and least-privilege enforcement
Legacy authentication protocols (POP, IMAP, SMTP AUTH)
Directory synchronization configuration (Entra ID Connect)
Shared account usage
Questions to Ask
How are user access rights assigned and reviewed?
Are legacy authentication methods disabled?
How often are access rights audited?
Documents to Collect
User and role assignment export
Authentication method policy configuration
2. Azure AD (Entra ID) Configuration
Items to Check
Tenant security settings
Custom domains and DNS configuration
Admin role assignments
Secure Defaults status
Questions to Ask
Who manages Entra ID security?
Are Secure Defaults or Conditional Access used?
How are admin roles monitored?
Documents to Collect
Entra ID tenant configuration export
Admin role assignment list
3. Multi-Factor Authentication (MFA)
Items to Check
MFA enforcement for all users
MFA enforcement for privileged roles
Authentication methods allowed (SMS, app, FIDO2)
MFA exclusion policies
Questions to Ask
Is MFA mandatory for all users and admins?
Are any users excluded from MFA?
What MFA methods are allowed?
Documents to Collect
MFA policy screenshots
Authentication method policy export
Items to Check
Azure AD PIM enabled
Role activation approvals
Just-In-Time access configuration
Role activation logs
Questions to Ask
Are admin roles permanent or just-in-time?
How are privileged roles reviewed?
Who approves elevated access?
Documents to Collect
PIM configuration report
Privileged role assignment logs
949-777-5567
Support@OCsecurityAudit.com
Irvine, California
Items to Check
Joiner, mover, leaver (JML) process
Disabled or stale accounts
Guest user lifecycle
Shared mailbox usage
Questions to Ask
How are users onboarded and offboarded?
How quickly is access removed after termination?
How are guest users reviewed?
Documents to Collect
HR onboarding/offboarding procedures
Disabled and guest user reports
6. Conditional Access Policies
Items to Check
Coverage for users and admins
Location-based access controls
Device compliance enforcement
Risk-based sign-in policies
Questions to Ask
What conditions restrict access to Microsoft 365?
Are risky sign-ins blocked or challenged?
Are exceptions documented?
Documents to Collect
Conditional Access policy export
Sign-in risk reports
7. Email Security (Exchange Online)
Items to Check
Anti-spam and anti-malware policies
Anti-phishing configuration
DKIM, SPF, and DMARC settings
Mail flow rules and transport rules
Questions to Ask
How do you protect against phishing?
Is DMARC enforced?
Are users trained to report phishing?
Documents to Collect
Exchange Online protection policies
DNS records for email security
8. Microsoft Defender for Office 365
Items to Check
Safe Links configuration
Safe Attachments policies
Anti-phishing impersonation protection
Alert policies
Questions to Ask
Which Defender features are licensed and enabled?
How are phishing alerts handled?
Are attack simulations performed?
Documents to Collect
Defender policy configuration exports
Alert and incident reports
949-777-5567
Support@OCsecurityAudit.com
Irvine, California
Items to Check
DLP policies across Exchange, SharePoint, OneDrive, Teams
Sensitive information types
Policy enforcement mode
Alert thresholds
Questions to Ask
What sensitive data is protected?
Are policies enforcing or audit-only?
How are DLP incidents reviewed?
Documents to Collect
DLP policy configuration
DLP incident logs
10. Information Protection & Sensitivity Labels
Items to Check
Sensitivity label configuration
Encryption settings
Auto-labeling policies
User adoption and usage
Questions to Ask
How is sensitive data classified?
Are labels mandatory?
Is encryption automatically applied?
Documents to Collect
Sensitivity label configurations
Label usage reports
Items to Check
External sharing settings
Site-level permissions
Anonymous link usage
Versioning and auditing
Questions to Ask
Who can share SharePoint content externally?
Are permissions reviewed regularly?
How is sensitive data protected?
Documents to Collect
SharePoint admin settings
External sharing reports
Items to Check
External sharing controls
Access expiration policies
Ransomware detection and recovery
Audit logging
Questions to Ask
How is OneDrive sharing controlled?
Are recovery options tested?
How long is data retained?
Documents to Collect
OneDrive admin configuration
Sharing activity logs
13. Microsoft Teams Security
Items to Check
Guest access policies
External access configuration
Meeting and messaging policies
File sharing controls
Questions to Ask
Are external users allowed in Teams?
How are meetings secured?
Are chats and files audited?
Documents to Collect
Teams admin policies
Guest access configuration
14. Endpoint Integration (Intune)
Items to Check
Device enrollment status
Supported platforms
Visibility of managed devices
MDM authority configuration
Questions to Ask
Are devices centrally managed?
Which devices can access Microsoft 365?
Is BYOD allowed?
Documents to Collect
Intune device inventory
Enrollment policy configuration
949-777-5567
Support@OCsecurityAudit.com
Irvine, California
Items to Check
Compliance policies
Encryption enforcement
OS and patch compliance
Conditional Access integration
Questions to Ask
What makes a device compliant?
Are non-compliant devices blocked?
How are compliance violations handled?
Documents to Collect
Compliance policy reports
Non-compliant device list
Items to Check
Unified Audit Log enabled
Log retention period
Admin activity logging
User activity monitoring
Questions to Ask
How long are logs retained?
Who reviews audit logs?
Are logs used for investigations?
Documents to Collect
Audit log configuration
Sample audit log exports
17. Incident Response & Alerting
Items to Check
Security alert policies
Incident response workflow
Escalation procedures
Post-incident reviews
Questions to Ask
How are security incidents detected?
Who responds to incidents?
Are incidents documented?
Documents to Collect
Incident response plan
Recent incident reports
18. Third-Party App Integrations
Items to Check
OAuth app permissions
Consent policies
High-risk app detection
App review frequency
Questions to Ask
How are third-party apps approved?
Are permissions reviewed regularly?
Are unused apps removed?
Documents to Collect
Enterprise application list
OAuth consent reports
Items to Check
Microsoft 365 retention policies
Backup solutions (native or third-party)
Recovery testing
Legal hold configuration
Questions to Ask
How is Microsoft 365 data backed up?
Are restores tested?
What is the retention period?
Documents to Collect
Retention policy configuration
Backup solution documentation
Items to Check
Regulatory requirements (HIPAA, SOC 2, ISO, etc.)
eDiscovery configuration
Retention labels
Governance policies
Questions to Ask
Which compliance frameworks apply?
How is compliance monitored?
Who owns governance?
Documents to Collect
Compliance policies
eDiscovery and retention reports
949-777-5567
Support@OCsecurityAudit.com
Irvine, California

User and Administrative Access
Review global and privileged admin accounts.
Audit all user accounts, including inactive and guest accounts.
Validate Multi-Factor Authentication (MFA) enforcement and compliance.
Assess Conditional Access policies for effectiveness and coverage.

Email and Exchange Security
Evaluate anti-spam, anti-phishing, and anti-malware policies.
Audit DKIM, SPF, and DMARC records for proper email authentication.
Review mailbox rules, forwarding, and delegation settings.
Identify sensitive information exposure through email.

SharePoint, OneDrive, Teams
Review external and guest sharing settings.
Audit site and file-level permissions for SharePoint and OneDrive.
Check Teams guest access, meeting, and file sharing policies.
Evaluate retention policies, DLP, and sensitivity labels for compliance.

Security and Compliance Tools
Assess Microsoft Secure Score and Compliance Manager scores.
Audit logging and alert configurations.
Evaluate application permissions and installed apps.
Check for adherence to regulatory requirements (HIPAA, ISO 27001, etc.).

Reporting & Recommendations
Document audit findings with risk prioritization.
Provide actionable remediation steps.
Present a summary report with executive-level highlights and technical details.

Audit Deliverables
Audit Findings Report: Detailed documentation of security gaps, risks, and misconfigurations.
Remediation Recommendations: Step-by-step guidance for resolving identified issues.
Executive Summary: High-level overview for management.
Optional Follow-up Review: Verification of remediated controls (if requested).
949-777-5567
Support@OCsecurityAudit.com
Irvine, California







OC Security Audit
Cybersecurity Services in Orange County, CA
We are proud to expand our Cybersecurity Services to additional cities within Los Angeles County, including Long Beach
- No matter where your business is located, we can assist you promptly.